-
Notifications
You must be signed in to change notification settings - Fork 574
[Examples] Deploy Identity Resources
This page describes how to deploy your Azure landing zone with the Identity resources created in the current Subscription context, using the default configuration settings.
Unlike the connectivity and management solutions, no resources are currently deployed when enabling deploy_identity_resources.
Instead, the Policy Assignments associated with the identity Management Group are enabled and configured based on the optional configure_identity_resources input variable.
The module will also move the Subscription specified in subscription_id_identity to the identity Management Group, unless it is the same value specified in subscription_id_connectivity or subscription_id_management.
In this example, we take the default configuration and make the following changes:
- Set
deploy_identity_resourcesto enable configuration of Policy Assignments associated with theidentityManagement Group. - Set the
subscription_id_identityvalue to ensure the Subscription is moved to the correct Management Group, and policies are updated with the correct values.
The module updates the parameters and enforcement_mode for a number of Policy Assignments, to enable features designed to protect resources in the identity Subscription including:
- Disable creation of Public IP resources;
- Disable RDP connectivity from the Internet;
- Enforce NSG on Subnets;
- Enable Azure Backup for VMs;
IMPORTANT: Ensure the module version is set to the latest, and don't forget to run
terraform initif upgrading to a later version of the module.
To create the Identity resources, deploy_identity_resources must be set to true, and the subscription_id_identity is also required.
TIP: The exact number of resources created depends on the module configuration, but you can expect upwards of 180 resources to be created by the module for this example.
To keep this example simple, the root module for this example is based on a single file:
main.tf
# We strongly recommend using the required_providers block to set the
# Azure Provider source and version being used.
terraform {
required_providers {
azurerm = {
source = "hashicorp/azurerm"
version = "~> 3.107"
}
}
}
provider "azurerm" {
features {}
}
# You can use the azurerm_client_config data resource to dynamically
# extract connection settings from the provider configuration.
data "azurerm_client_config" "core" {}
# Call the caf-enterprise-scale module directly from the Terraform Registry
# pinning to the latest version
module "enterprise_scale" {
source = "Azure/caf-enterprise-scale/azurerm"
version = "<version>" # change this to your desired version, https://www.terraform.io/language/expressions/version-constraints
default_location = "<YOUR_LOCATION>"
providers = {
azurerm = azurerm
azurerm.connectivity = azurerm
azurerm.management = azurerm
}
root_parent_id = data.azurerm_client_config.core.tenant_id
root_id = "myorg"
root_name = "My Organization"
deploy_identity_resources = true
subscription_id_identity = data.azurerm_client_config.core.subscription_id
}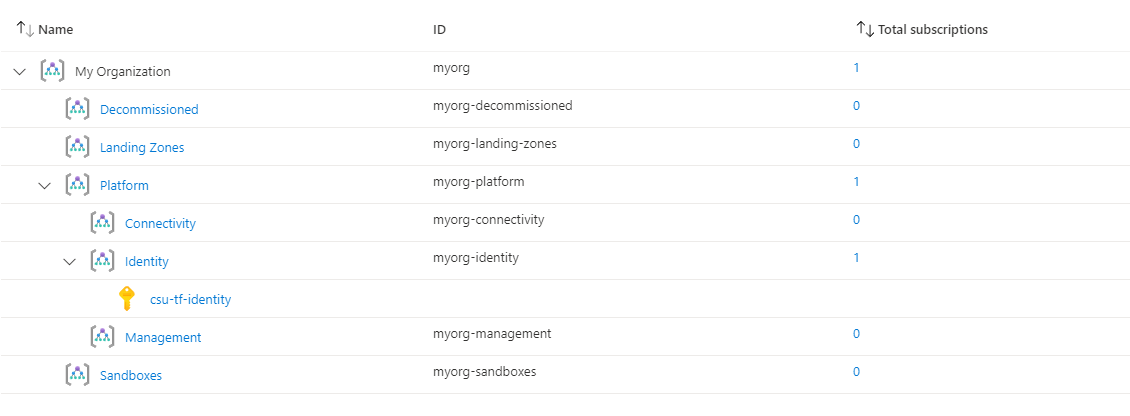
You have successfully created the default Management Group resource hierarchy, along with the recommended Azure Policy and Access control (IAM) settings for your Azure landing zone.
You have also assigned the current Subscription from your provider configuration to the identity Management Group.
Check the following Policy Assignments to see how these have been configured with default settings for parameters and enforcement mode:
- Scope =
identityDeny-Public-IPDeny-RDP-From-InternetDeny-Subnet-Without-NsgDeploy-VM-Backup
You may want to Deploy Identity Resources With Custom Settings to change some of these settings.
The following shows the Deploy-VM-Backup Policy Assignment with a user-defined values set by the module for the parameters.
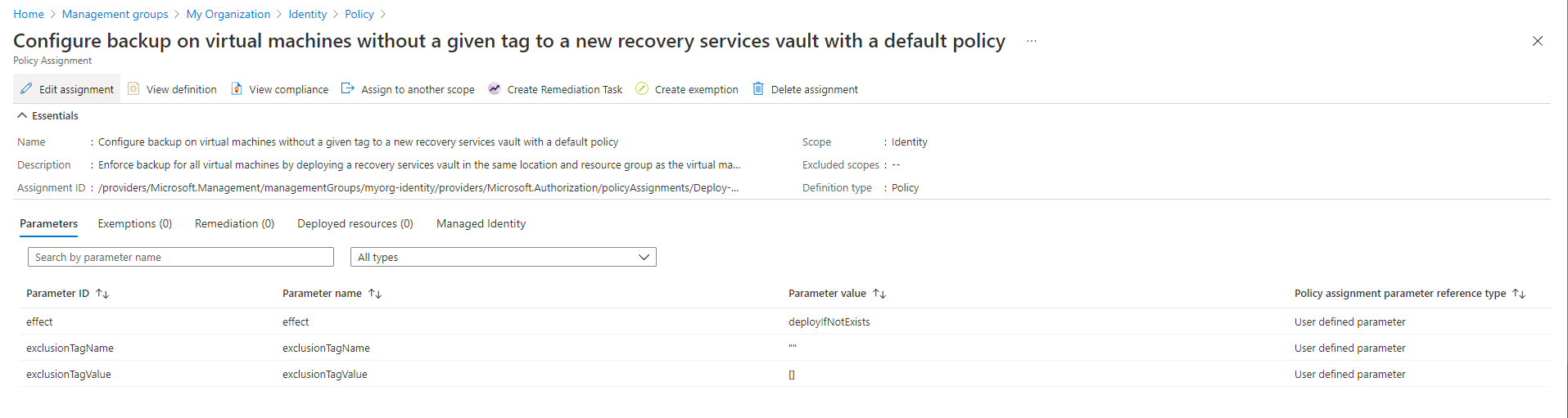
Unless you have deployed resources into the current Subscription context used for your deployment, there shouldn't be any resources reporting a compliance state.
No resources will be deployed in your identity Subscription by this module.
If you are using Archetype Exclusions or custom Archetypes in your code, make sure to not disable the managed policies (listed above) if you require policy integration using this module. The relationship between the resources deployed and the Policy parameters is dependent on specific Policy Assignments being used.
Go to our next example to learn how to deploy the Identity resources with custom settings.
To learn more about module configuration using input variables, please refer to the Module Variables documentation.
Looking for further inspiration? Why not try some of our other examples?
This wiki is being actively developed
If you discover any documentation bugs or would like to request new content, please raise them as an issue or feel free to contribute to the wiki via a pull request. The wiki docs are located in the repository in the docs/wiki/ folder.
- Home
- User guide
- Video guides
-
Examples
- Level 100
- Level 200
-
Level 300
- Deploy multi region networking with custom settings (Hub and Spoke)
- Deploy multi region networking with custom settings (Virtual WAN)
- Deploy with Zero Trust network principles (Hub and Spoke)
- Deploy identity resources with custom settings
- Deploy management resources with custom settings
- Expand built-in archetype definitions
- Create custom policies, initiatives and assignments
- Override module role assignments
- Control policy enforcement mode
- Policy assignments with user assigned managed identities
- Level 400
- Frequently Asked Questions
- Troubleshooting
- Contributing
